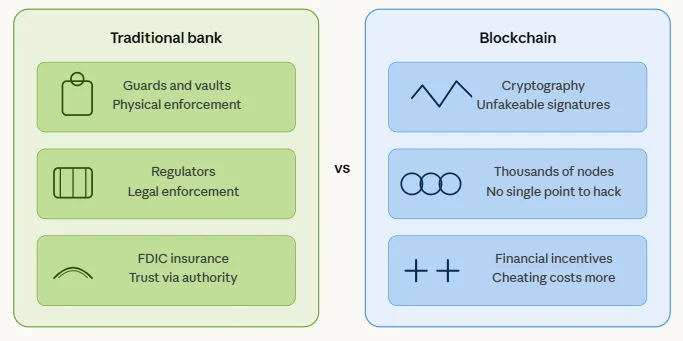
When someone deposits money at a bank, they trust it because of FDIC insurance, government oversight, and physical security. There’s an institution enforcing that trust – people in suits, legal frameworks, vaults. Blockchain has none of those things. No central authority, no regulator backing every transaction, no human at the top making sure it all works.
So how does it stay secure? In simple terms, blockchain economic security means the system is designed so that cheating costs more than it’s worth. Instead of trusting a bank, a government, or any middleman, you’re trusting math and financial incentives. Everyone who participates has a financial reason to play by the rules and a financial reason not to cheat. That’s the whole idea.
It sounds almost too simple, but it’s actually a pretty elegant design. Let’s break down how it works.
Blockchain economic security: The foundation of trust
The core idea is that participants in a network are kept honest not through rules or enforcement, but through financial incentives. Playing by the rules earns rewards. Breaking the rules is either too expensive to bother or results in the attacker losing more than they gain.
This is a fundamentally different model from traditional security. A bank uses guards and vaults. A blockchain uses math and money. The participants who validate transactions, known as miners or validators depending on the network, earn fees and rewards for doing their job correctly.
If they try to cheat, they risk losing those rewards and potentially destroying the value of the very currency they’re holding. A successful attacker who corrupts Bitcoin doesn’t walk away rich. They walk away holding an asset they just helped destroy.
Blockchain economic security works because the system makes honest behavior the most profitable choice, not because it forces people to be honest.
Crypto network security model: How three things work together
The crypto network security model rests on three interconnected pillars. Remove any one of them and the whole structure weakens.
Cryptography is the mathematical layer. Every transaction is locked with a digital signature that can’t be faked. Each block in the chain is linked to the one before it, making it nearly impossible to alter the history without being detected.
Decentralization spreads copies of the same record across thousands of computers worldwide. There’s no single server to hack. An attacker would need to overpower the majority of the entire network simultaneously.
Consensus is the agreement layer. All those computers must agree that a transaction is valid before it’s added to the chain. No single participant can write whatever they want into the record.

The crypto network security model only works when these three elements function together, because each one reinforces the others.
A chain with strong cryptography but heavy centralization is still vulnerable – the decentralization pillar is what makes attacking the other two economically prohibitive. That’s exactly what the 51% attack exploits.
The 51% attack: The most direct threat to network security
The biggest test of economic security is something called a 51% attack. Understanding it explains why network size matters so much in crypto.
A 51% attack happens when a single person or group gains control of more than half of a blockchain network’s total computing or staking power. With that majority control, they can manipulate which transactions get recorded and even reverse transactions that have already been confirmed.
The practical result of this is double-spending. Someone sends a large amount of crypto to an exchange, converts it to something else, withdraws it, and then uses their majority network control to erase the original transaction from the record. The exchange loses the funds. The attacker keeps both what they withdrew and the original crypto.
Proof-of-Work: Security through physical cost
Bitcoin uses a system called Proof-of-Work. To validate transactions, computers on the network compete to solve complex mathematical problems. The first to solve it earns the reward and adds the next block. The more computing power a participant has, the better their odds.
To attack Bitcoin this way, an attacker would need more computing power than everyone else on the network combined. Research puts the cost of assembling that much computing power at over $6 billion, a figure that makes the attack economically irrational for almost any potential attacker.
The problem is that smaller cryptocurrencies using the same system don’t have that protection. A 2026 study published in Complex & Intelligent Systems found that while established blockchains like Bitcoin require attack costs exceeding $6 billion, newer chains with smaller participation can be compromised for as little as $50,000 to $1 million. The difference comes down entirely to scale.
Proof-of-Stake: Security through financial stakes
Ethereum and most modern blockchains take a different path entirely. Rather than burning electricity to compete for the next block, participants in a Proof-of-Stake system put up their own money instead. Validators lock up a set amount of cryptocurrency as collateral before they’re allowed to do anything. That locked amount is called a stake, and it’s what earns them the right to validate transactions.
This changes the attack math significantly. Pulling off a 51% attack on Ethereum means the attacker has to actually own more than half of all the ETH currently staked on the network.
We’re talking about accumulating a position large enough that the buying pressure alone would drive the price up and make the whole thing progressively more expensive to execute. And because it happens on a public ledger, the network sees it coming.
There’s also a built-in punishment mechanism called slashing. Get caught cheating, and the network doesn’t just reject you. It destroys part or all of your staked tokens.
So the attacker doesn’t just walk away empty-handed. They lose the capital they put in to attempt it. That’s what makes large Proof-of-Stake networks so difficult to attack in practice.
Why smaller coins carry more risk
The same principles that protect Bitcoin and Ethereum work against smaller cryptocurrencies. A coin with a small number of participants and a low total market value is simply cheaper to attack.
Bitcoin Gold is a clear example. In May 2018, attackers used rented hashing power to execute a 51% attack and double-spend approximately $18 million worth of BTG across several exchanges. Bittrex later delisted the coin.
Ethereum Classic’s story is similar. In August 2020, the network was hit by three separate 51% attacks in a single month. In the most analyzed of those attacks, the attacker double-spent over $5.6 million worth of ETC while spending only around $192,000 to acquire the necessary hash power from NiceHash – a 2,800% return on the cost of the attack.
The math was simple: the attack cost a fraction of what it returned. After the attacks, ETC Labs implemented new defensive measures, but the reputational damage was lasting. Several exchanges tightened confirmation requirements or suspended ETC deposits entirely.
These weren’t technical hacks in the traditional sense. They were economic calculations. The cost of the attack was lower than the potential reward, so the attacks happened. When the math flips, attacks stop making sense.
What this means for anyone holding crypto
For someone new to crypto, this framework provides a useful filter. Large, established networks with high participation and substantial amounts staked or mined are significantly harder to attack. Smaller or newer coins offer less of that protection.
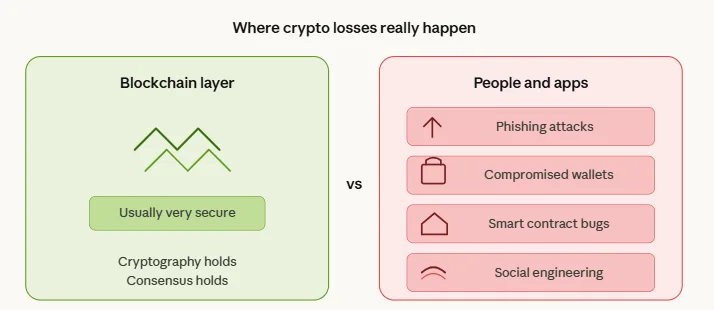
It’s also worth understanding that the blockchain layer is typically the most secure part of the system. Most real-world crypto losses stem from other sources entirely, such as phishing schemes, compromised wallets, smart contract bugs, and social engineering.
The chain itself is usually the last place a sophisticated attacker bothers with, because the math there is settled. What isn’t settled is everything built on top of it: the wallets, the apps, the people using them. That’s where good personal security practices matter most.