Crypto trading has developed far beyond the process of just buying and selling tokens. Today, traders explore new projects, interact with decentralized platforms, and operate nodes. Each of these actions leaves small traces online, and over time, those traces can reveal more than most people realize.
For traders who value privacy, controlling how their data appears to the outside world has become just as important as securing their wallets. A tool like Tor offers a different approach to browsing by changing how internet connections occur. When used properly, Tor reduces the amount of information that platforms or attackers can link back to a user.
What is Tor, and how does it work?
The Onion Router (Tor) is a privacy-focused network that masks connections, preventing the revelation of user data to the outside world. This network often reroutes network traffic through volunteer-focused serves hence disguising the origin of a network connection.
Tor is built around layered encryption, which has seen it referred to as an “onion” network. It wraps information into several layers prior to leaving the user’s computer, and the relay removes only the needed layer before forwarding the traffic.
Consequently, none of the relays has full information about the sender or the ultimate destination. In crypto, this helps mask crypto transactions from public eyes and malicious actors. Tor circuits typically consist of three relays, each with distinct functions in moving data through the network:
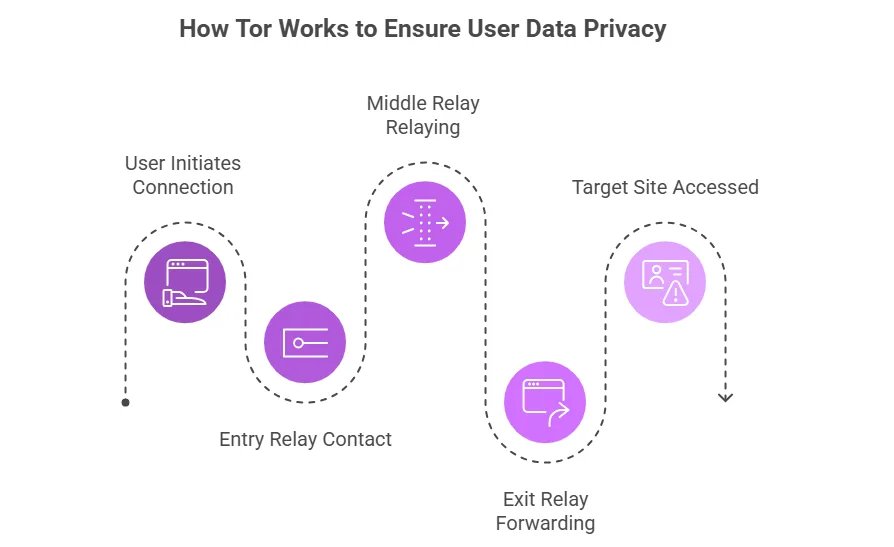
- Entry relays are the point of the first contact and are aware of the IP address of the user, but not the destination.
- Middle relays relay encrypted traffic over the circuit without knowing the source or the destination point.
- Exit relays forward the request to the target site, and the site is accessed, but not the user.
Such a design minimizes the chances of a single node completely identifying the user on a connection. Circuits also periodically rotate on the network, and this further complicates any attempts made to track Circuits over a long period.
To crypto traders, this implies that whenever they connect to a platform via Tor, the platform usually appears to have the IP address of the exit relay and not the location of the trader on the network.
How traditional browsers expose crypto users
The majority of individuals use crypto services using normal browsers, just like any other webpage. These browsers are not designed with the main aim of anonymity, although they are convenient. Every time a trader visits a platform, several pieces of information become visible on the website.
IP addresses are one of the most obvious signals. A crypto trading platform can detect the network location of the connection and record it as part of account activity. Even if the user changes wallets, repeated connections from the same location can slowly build a recognizable pattern.
Browser fingerprinting is also another exposure. Websites are able to collect technical information on the device and blend it to form a unique identifier. With time, this fingerprint can enable platforms of analytics tools to identify the same user in multiple visits.
Typical methods in which standard browsing environments expose crypto users include:
- Websites identify the IP address used by a user to log in, make trades, or even link their wallets.
- Device fingerprinting is formed by browser configuration, operating system, and display settings.
- Tracking scripts embedded in crypto platforms that record session behavior.
- Network patterns that link multiple wallets or accounts to the same user over time.
These signals can lead to a slow erosion of the perceived anonymity of traders who have to make regular transactions across exchanges or other decentralized applications (dApps).
How to use Tor to conceal crypto trading activities effectively
The following are some of the general practices that traders must adhere to to incorporate Tor into their workflow:
- Use the Tor Browser to access exchanges, crypto interfaces, and research sites.
- Use different individual wallets or accounts for various trading opportunities.
- Refrain from accessing personal services in the same Tor session used to trade.
- Renew the Tor identity often so as to rotate circuits and decrease tracking patterns.
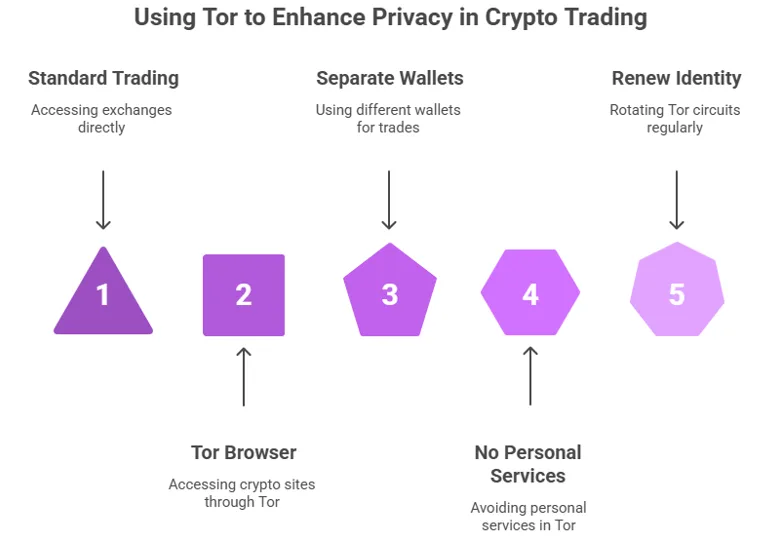
Additionally, users must avoid customizing their Tor browser too much. Tor is also specifically set up to make most users look alike. This makes fingerprinting more difficult, but adjusting too many settings can accidentally form an exclusive profile.
Why privacy matters in crypto trading
Crypto tries to strike a balance between an open and closed system. Transactions through blockchains are public in nature, although most traders do not want their names to be associated with what they have or how they trade. The risks are high once the activity of a wallet is associated with a real person.
In most instances, targeted attacks often emerge from a user’s wallet activity being known to malicious actors. Phishing attacks, scams, or efforts to monitor the online actions of high-value crypto players, analysts, or other prominent personalities are common targets of phishing attacks. Attackers do not necessarily require actual access to the wallet; at times, it is sufficient to locate a user or the device details in order to start profiling.
Regulation and data collection make this problem more complicated. Many trading platforms collect metadata such as IP addresses, login history, and device fingerprints as part of their monitoring systems. While some of this is intended for security, it still creates a record that can connect trading activity to a specific user.
In addition, early-stage projects and token launches attract a large number of participants. Traders trying to access presales or new opportunities may prefer not to reveal their network identity during the process. Privacy tools help reduce the risk of being tracked across different platforms or trading sessions.
Which crypto wallets and coins use Tor?
Several crypto ecosystem tools have been built over the years with Tor support. Such integrations enhance privacy in the transmission of transactions in blockchain networks. This compatibility makes a big difference to users who wish to reduce their exposure.
Additionally, some wallets and services automatically direct traffic via Tor, while others allow the user to do so manually. The aim is, in most instances,s to deny other participants on the network the ability to determine the original point of transaction or node operation.
Examples of crypto tools and environments that support Tor include:
- Bitcoin nodes that are set to communicate with peers via the Tor network.
- Wasabi Wallet, which uses Tor by default to protect transaction broadcasting.
- Samourai Wallet tools that integrate Tor routing for enhanced privacy features.
- Some decentralized services that host .onion versions of their services.
These applications enable users to interact with blockchain networks without necessarily disclosing their connection information to other users. The blockchain is a transparent network, but network-level privacy is an added benefit.
Final thoughts
Tor is one of the greatest privacy technologies on the internet, particularly for crypto communities that value financial sovereignty. Using conventional tools in trading can give away sensitive information. But using Tor for trading-related activities can help mask your internet connections and thus minimize risks such as phishing attacks.
However, Tor alone does not offer a comprehensive solution. Traders can combine it with other security-focused solutions, such as using different wallets and browsing cautiously to achieve maximum security or privacy.