Blockchain systems have a well-known vulnerability known as a 51% attack. However, this attack has nothing to do with wallet hacking or the cracking of encryptions. Rather, it is a risk that stems from miners gaining too much control of a blockchain network’s hash rate. Let’s explore what this risk is all about.
What is a 51% attack in blockchain?
To answer the question ‘what is a 51% attack?’ we first need to understand how a Proof-of-Work (PoS) blockchain works since the attacks are more hinged on blockchains that use this consensus mechanism.
Miners compete to solve some mathematical computations necessary to validate transactions in a proof-of-work blockchain. To add new blocks to a blockchain, every miner needs a lot of computing power, which is called hash rate. Miners who have more computing power usually solve these puzzles faster, which lets them add new blocks first.
Now that you understand how a PoW blockchain works. Let’s explain what a 51% attack on a blockchain is!
A 51% attack on a blockchain is a scenario where a miner, or a group of miners, gains more than 50% of the aggregate hash rate. This majority gives the entity or group the capability of producing blocks quicker than all the rest put together. This means that these miners can take advantage to affect the transactions that are accepted or rejected on the network.
However, the control gained from controlling over 50% of the hash rate does not come with unlimited power. Malicious individuals cannot retrieve private keys or steal assets from user wallets. Nor can they alter protocol rules.
What they can do, however, is control how transactions are managed on the network. These actors can change the order of transactions to be processed. This control of order blocks results in big network issues affecting how transactions are finalized.
The mechanism of a 51% attack
A 51% attack stems from the control of block production. In normal instances, miners usually operate independently, making it difficult to determine who will mine the next block. This uncertainty is what makes the mining process fair.
But once an attacker possesses the majority of the hash rate, then the balance and fairness disappear. These miners gain the capability to mine the blocks faster than the rest of the miners on the network.
A 51% attack typically follows a defined structure:
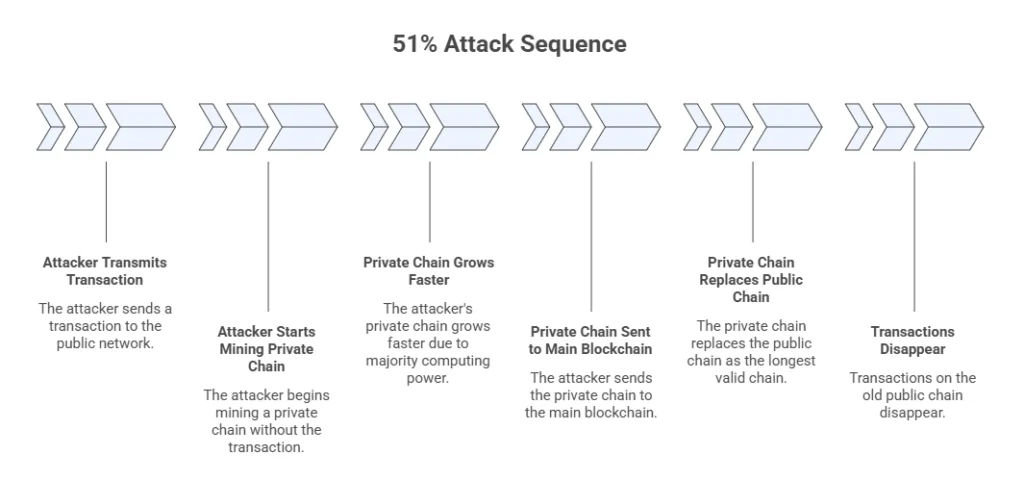
- The attacker transmits a transaction to the public network, often to purchase items or remit funds to an exchange.
- Concurrently, they start mining a chain that is privately owned, where such a transaction does not exist.
- Since the attacker operates the majority of the network’s computing power, their private chain grows faster.
- The actors then send the private chain to the main blockchain once it grows longer than the public chain.
- As a result, the attacker’s chain replaces the public chain since blockchains accept the longest valid chain.
- Once that happens, transactions on the old chain disappear, even if they were confirmed.
This operation breeds double-spending, since the attacker can retain the goods and original assets used for the initial transaction. While the network does not fail technically, transaction results are compromised.
In addition to double-spending, the attacker may also delay or halt new transactions on the network. The attacker might also activate censorship of individual users or addresses by determining the transactions to incorporate in their blocks.
Risk of a 51% attack
The 51% attack risk is tied to the extent of harm that can be caused before the network fixes the issues. Even a short-term attack could result in loss of trust and financial loss. In that case, some of the risks of a 51% attack include:
- Double-spending: This is one of the direct risks that result from a 51% attack. It mostly impacts crypto exchanges and merchants who depend on accurate transaction records. If an attacker double-spends, these players stand to lose in a financial sense.
- Transaction censorship: The other risk associated with a 51% attack is transaction censorship. The attacker may decline to add some transactions to blocks, thus preventing users from making transactions or moving funds from one wallet to another. This renders part of the affected blockchain network inoperable.
- Network instability: Another risk from a 51% attack is network instability. If the attackers reorganize the network often, then reliance on transaction finality fades out. This may trigger mistrust and conflict once confirmed transactions start disappearing from the network.
Which networks are more prone to 51% attacks?
The risk of a 51% attack stems from a blockchain’s overall hash rate. This means that a network with a low hash rate is easier to manipulate by 51% attackers than one with a high hash rate.
In small networks, mining is usually concentrated among small actors. If one miner gets too big, to the point of controlling 51% of the hash rate, this poses the risk of a 51% attack.
In some instances, malicious miners may rent out computing power to perform a 51% attack on an on-demand basis before releasing the resources.
That said, a 51% attack can happen on any blockchain network. However, the key parameter to determine whether a blockchain can be attacked by malicious miners is its hash rate.
Prevention of a 51% attack
A 51% blockchain attack doesn’t have a definite prevention method. However, some of the options implemented include:
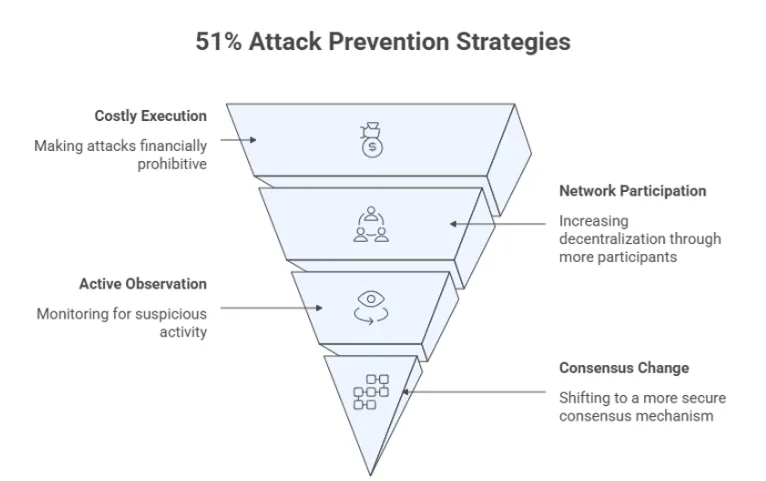
- Making it too expensive to execute: Some blockchains try to make 51% attacks costly and risky enough to execute, thus curbing them.
- Amplifying network participation: The greater the number of miners or validators, the less control would be obtained by any party. This makes networks with more validators less prone to such attacks.
- Active observation: Early detection of 51% attacks can be achieved by flagging spikes in hash rate or strange reorganization of chains. Early warning can help the exchanges and users to take caution, like waiting to get more confirmations.
- Changing the consensus mechanism: Proof-of-Stake systems require validators to stake tokens as opposed to utilizing the computing power. Changing to a PoS model, it makes it difficult for attackers to control huge proportions of the total supply needed to control the network. However, this is viable in extreme scenarios.
Conclusion
A 51% attack is not a wallet or encryption hacking attack, but rather an attack that allows miners with 51% of the total hash rate or more to control how transactions are added to the block at particular times. From this attack stems risks such as double-spending, which affects merchants and exchanges, transaction censorship, and network instability.
Some of the ways to prevent this type of attack include fostering decentralization, making it expensive to attack the network by raising the rate of hash or staking, active network surveillance, and, in extreme instances, changing the blockchain’s consensus mechanism, like in the case of Ethereum, which successfully transitioned from Proof-of-Work to Proof-of-Stake back in September 2025.