Imagine building the most transparent financial system in human history, where every transaction is recorded forever on a public ledger, and then losing $17 billion anyway. Welcome to the wonderful, chaotic, occasionally catastrophic world of crypto hacks, where the vault is made of math but the keys are held by humans, and humans, bless them, keep clicking phishing links.
This is not another dry list of numbers. This is the story of how some of the biggest digital heists happened, why they keep happening, and how you can avoid becoming the next cautionary tale. Pull up a chair.
So who is actually stealing all this money?
Meet the main villain: North Korea. The Lazarus Group, a state-sponsored hacking collective, has been fingerprinted at several of the biggest blockchain robberies in recent memory. In 2025 alone, crypto hackers stole $3.3 billion, with supply-chain breaches emerging as the most damaging threat, accounting for $1.45 billion in losses across just two incidents, including the $1.4 billion Bybit hack. And 2026 is not doing much better.
The industry has already lost over $600 million to hacks in 2026, largely due to two North Korea-linked crypto thefts in April, including the $293 million Kelp DAO exploit and the $280 million exploit of the Drift Protocol.
One of the attackers even used artificial intelligence for social engineering. Not robots stealing crypto, but AI-assisted con artists building fake personas to trick real humans into handing over access. Satoshi did not see that coming.
Eight heists that rewrote the rulebook
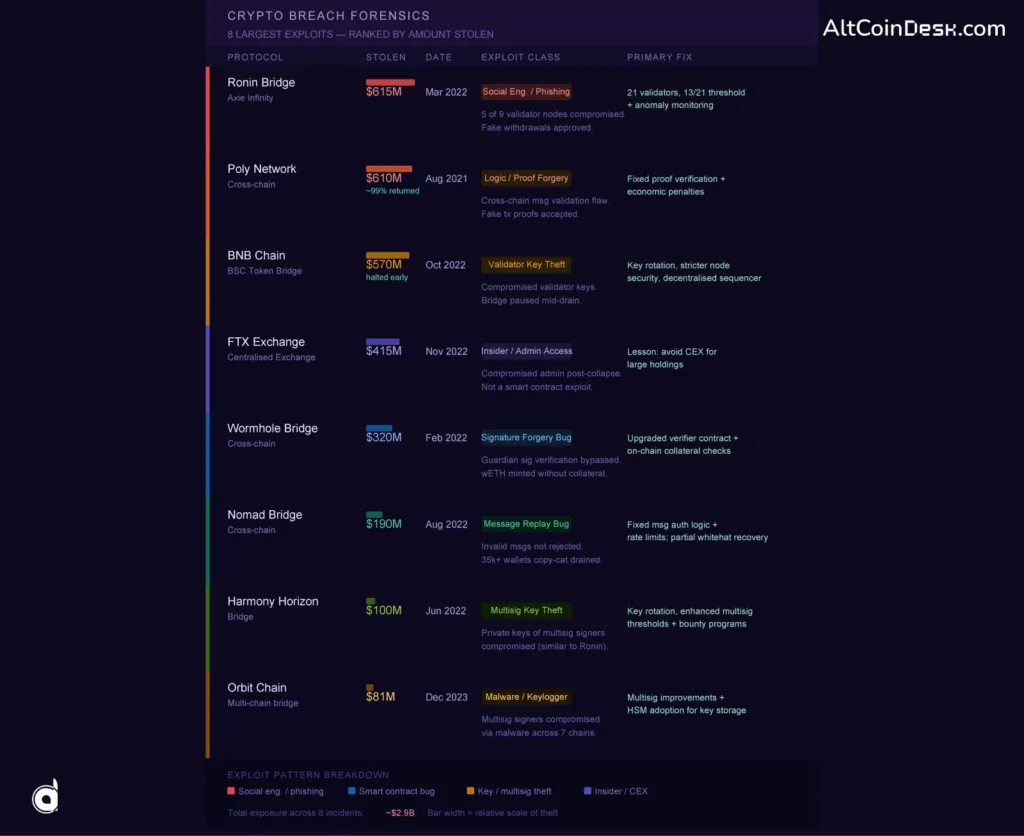
The Ronin robbery nobody noticed for six days
March 2022. Axie Infinity’s Ronin Bridge got cleaned out of 173,600 ETH and 25.5 million USDC, roughly $615 million. The method? No alien technology required. Hackers created fake LinkedIn job offers, phished a Sky Mavis employee, crawled through internal servers, and eventually compromised five of the nine validator nodes needed to approve withdrawals.
The fake transactions looked perfectly legitimate because they were correctly signed. Nobody noticed for six days, until a user tried to withdraw funds and found the cupboard bare. The lesson is brutal: a multisig system sounds secure until five of those validators are controlled by the same office and one convincing LinkedIn recruiter.
Wormhole: When the maths lies
February 2022. The Wormhole bridge lost $320 million to a signature verification bug. The attacker forged the bridge’s approval stamp, convincing the system that 120,000 wrapped ETH had been properly deposited when nothing had been locked as collateral.
It is the crypto equivalent of writing yourself a cheque from an account that does not exist and having the bank honor it. Jump Trading covered the full loss. Not everyone gets that lucky.
Nomad: The crowd-sourced bank robbery
August 2022. Nomad Bridge lost $190 million, but the truly stomach-dropping part is how it unravelled. One attacker found a message authentication bug. Within hours, over 300 wallets, mostly opportunists watching blockchain activity in real time, copied the exact same exploit. You did not even need to understand it; you just changed one wallet address and submitted the same transaction. A $190 million mistake turned into an open invitation.
Poly Network: The one that came back
The $610 million Poly Network hack of 2021 deserves its own chapter because the attacker returned nearly everything. A cross-chain message validation flaw allowed fake transaction proofs to pass through undetected. The hacker drained it, got identified, had a philosophical exchange with the team over Twitter, and sent back 99% of the funds. On this list, that practically qualifies as a happy ending.
The rest of the hall of shame
Harmony Horizon Bridge lost $100 million in June 2022 through compromised private keys on its multisig, with only about 5% ever recovered. BNB Chain faced a $570 million risk in October 2022, but the chain was paused before the full drain, proving that a fast response actually matters.
FTX saw $415 million disappear during its November 2022 bankruptcy collapse through what appeared to be insider access, with no smart contract involved at all. On New Year’s Eve 2023, Orbit Chain’s multisig signers were targeted by malware and keyloggers while the world counted down to midnight, costing $81 million across seven chains.

The pattern hiding in plain sight
Look at every single one of these incidents, and a theme emerges: approximately 70% of major blockchain thefts involve compromised private keys or flawed bridge multisig setups. The blockchain code is often fine. The humans holding the keys are the vulnerability.
The average size of crypto hacks rose to $19.5 million in 2025, meaning attackers are not getting lazier; they are getting more selective. Starting in late 2025 and into 2026, the attack landscape shifted noticeably toward individuals with large holdings rather than purely protocol-level exploits. Whales are now being stalked on-chain, identified, and then targeted. One trader lost $24 million in early 2026 in an attack that started as an address poisoning scam and reportedly escalated into a physical confrontation. The blockchain is secure. The person sitting behind it is considerably less so.
Bridges: Where crypto goes to get robbed
Of every attack surface in the ecosystem, bridges are the most consistently catastrophic. They lock assets on one chain and mint equivalent tokens on another, which sounds elegant in a whitepaper and terrifying in practice, because one smart contract holds enormous value and one bad line of code can drain all of it.
The Kelp DAO exploit in April 2026 drained 116,500 rsETH, about $292 million, and roughly 18% of the token’s circulating supply, making it one of the largest DeFi exploits of the year. One trust assumption. Nearly $300 million. Bridges remain, as one security researcher put it, a gift that keeps on giving, mostly to attackers.
The industry is responding. Bridges are increasingly moving toward zero-knowledge proof verification, which removes the trusted validator bottleneck entirely by using cryptography to confirm an asset genuinely exists on the source chain before minting anything on the destination. Slower to build, considerably harder to drain.

Hardware wallets: Your best boring defence
Against all the drama of validator compromises and supply chain attacks, the hardware wallet remains stubbornly effective. Private keys never leave the device, meaning remote malware, phishing links, and clipboard hijackers all hit a dead end. Physical button confirmation means a fake transaction screen cannot simply trick you into signing away everything.
A practical personal security framework: A hardware wallet for long-term holdings, less than 5% of your portfolio in hot wallets for active use, app-based two-factor authentication rather than SMS on every exchange, no unlimited token approvals, and treat every unsolicited airdrop DM as a potential mugging. These steps eliminate the vast majority of losses described across the major blockchain heists above.
What 2026 is teaching us the hard way
April 2026 became a case study in how fast DeFi security failures escalate. Two exploits in 18 days wiped out $577 million, and the year-to-date total sits at $771.8 million with more than seven months still to go.
The US Department of the Treasury announced it is expanding its cybersecurity threat identification program to cover digital assets. AI-driven anomaly monitoring, MPC wallets, and quantum-resistant cryptographic curves are all moving from buzzword territory into actual deployment.
The tools are improving. So are the attackers. The real question is which side has the faster learning curve.
The uncomfortable takeaway
Blockchain technology did not fail in any of these incidents. Cryptography held. The distributed ledger worked exactly as intended. What failed, repeatedly and expensively, was the human layer: the employee who clicked a LinkedIn link, the developer who skipped a verification step, and the exchange that never imagined an insider might walk off with the keys.
Blockchain security breaches have surpassed $17 billion over the past decade, with private key compromises as the leading cause. Seventeen billion dollars of largely preventable losses, mostly because someone, somewhere, trusted the wrong thing.
The blockchain remembers everything. Unfortunately, humans keep forgetting the same lessons. Until the industry builds systems that assume human failure and compensate for it accordingly, the heists will continue. The only real question is whether your funds are inside the vault or left on the counter when the next crypto exploit arrives.